This is part of a series of blogs diving into the technical aspects of Veridium’s distributed data model, biometrics, and computer vision research and development by our chief biometric scientist Asem Othman.
In the nineteenth century, Alphonse Bertillon, a French policeman, was the first to introduce the science of identifying a person based on his/her anatomical features. To identify repeat offenders, Alphonse built a set of tools known today as the Bertillon System. These tools were used to measure certain anatomical traits of a person including eleven different body measurements such as the height, length, and breadth of the head, the width of cheeks, the length of different fingers, the length of forearms, etc.

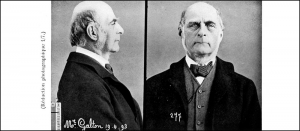
The image above shows an illustration of the process for acquiring the forearm measurements. These measurements were then recorded on an identity card, and/or were manually compared to a record database to check if the same person was convicted before. The system was used until 1903 when it was replaced by fingerprint records, but a few elements of the Bertillon System exist even today in the criminal police identification process, such as the combination of profile and frontal shots (mug shots) when photographing offenders.

Fingerprints as a Biometric
The complexity of the Bertillon System was the reason for providing criminal identification systems with accurate and reliable data, but it was also the reason for the system’s downfall. Therefore, the supremacy of the Bertillon System began to fade in the face of a new (at that time) identification technique – fingerprint identification, which was simpler to administer than the Bertillon anthropometry system. The use of fingerprints for establishing identity was started in the 16th century and thereafter replaced the Bertillon System as the worldwide standard for criminal identification.

A fingerprint refers to the flow of ridge patterns in the tip of the finger. The ridge flow exhibits irregularities in local regions of the fingertip termed as minutiae points. In 1892, Sir Francis Galton introduced the minutiae features for fingerprint matching. Since then, the distribution of these minutiae points along with the associated ridge structure has been believed to be distinctive to each fingerprint and has been used in individual identification records in police offices.
Fingerprints recognition systems are considered to be a reliable method to recognize individuals and are used in different biometric applications, such as physical access control, border security, watch list, background check, and national ID systems.
Representation and Matching
The uniqueness of a fingerprint is predominantly determined by the local ridge characteristics and their relationships, and matching fingerprints manually to claim that two impressions belong to the same person, requires complex protocols that have been used by examiners. Over the last three decades, research in fingerprint recognition has seen tremendous growth. However, most automatic fingerprint matchers follow similar protocols as human examiners and depend on the ridge characteristics of fingerprints. These characteristics (fingerprint features) can be organized in a hierarchical order at three different levels.
Level 1 features include the ridge flow, pattern type, external fingerprint shape, orientation image, and frequency image. Level 2 features consist of minutiae location and orientation. And, level 3 features consist of information available at higher resolution images, such as local shape of ridges, dots, pores and incipient ridges. On the basis of the described hierarchical order, fingerprint matching can be accomplished using three classes of matchers.

Fingerprint Level 1 Features Matchers
The matchers of this class compare the global pattern of ridges or correlation based matchers. During the matching procedures, the fingerprint or the global ridge orientation images are superimposed on each other and the correlation between the corresponding pixel intensities is computed for different alignments (various displacements and rotations). In general, it has been reported that the Level 1 features are useful for fingerprint classification and indexing, but not sufficient for fingerprint matching.
Fingerprint Level 2 Features Matchers
These are the most popular matchers whereby minutiae points are extracted from the fingerprint to be matched, and their location and ridge orientations are stored as a fingerprint template in a central database. The matching process determines the alignment between two minutiae sets that results in the maximum number of minutiae pairings. Some matchers utilize the Level 1 features, such as texture information, local orientation, frequency and/or ridge pattern, along with the extracted minutiae, to match two fingerprints.
Fingerprint Level 3 Features Matchers
This class of matchers is the least explored by researchers, compared to Level 2 features matchers. This is due to two major reasons; (1) robust extraction of level 3 features (ridge shapes, sweat pores) requires high resolution images (> 1,000 ppi – number of pixels per inch in the image) compared to 500 ppi (the current FBI standard), and (2) even with availability of good quality images, these matchers require high computational complexity. These reasons have made the practicality of using these matchers for some commercial applications debatable. However, Level 3 features play a significant role in latent fingerprint matching, where fingerprints are lifted from a surface prior to digitizing them.